BSI IT baseline protection tool HITGuard

At the heart of the BSI IT Baseline Protection Compendium are the so-called IT baseline protection modules. Each module deals with a topic and relevant safety aspects. If the requirements of a building block are not met, there are concrete recommendations for measures to counteract this. Together with the BSI standards, the BSI IT Baseline Protection Compendium forms a methodology for sound IT security management.
Our ISMS software HITGuard efficiently maps the requirements of the BSI IT Baseline Protection Compendium. HITGuard adapts flexibly to your individual needs. For example, many of our customers are interested in a combination of BSI IT baseline protection and ISO 27001. That's no problem either. HITGuard accompanies and supports you from the beginning to the submission of the certification documents.
Is the topic new to you or do you need support in the implementation, e.g. to achieve ISO 27001 certification? Our competent team will be happy to help you!

and Betriebsführungsges.m.b.H
Future-proof BSI baseline protection with HITGuard ISMS
BSI Grundschutz++ mit HITGuard im Blick
Das BSI entwickelt den IT-Grundschutz derzeit in Richtung Grundschutz++ weiter. TogetherSecure ist selbst Teil der Arbeitsgruppe und wird HITGuard für die Unterstützung von Grundschutz++ vorbereiten.
Wichtig: Der BSI Grundschutz++ ist aktuell noch nicht final und damit subject to change. Für den produktiven Einsatz sollten daher derzeit weiterhin die etablierten und stabilen Vorgaben des bestehenden IT-Grundschutzes herangezogen werden.
Mit HITGuard setzen Sie den heutigen BSI IT-Grundschutz bereits effizient um und schaffen zugleich eine gute Grundlage, um künftige Entwicklungen wie Grundschutz++ strukturiert aufzugreifen.
Highlights
- Licensed content of the BSI IT Baseline Protection Compendium
- Proposed measures for weaknesses found
- Easy determination of compliance coverage of Compendiums Chapters
- Annual update to the current Basic Protection Compendium
- Automatische Überführung bereits bewerteter Kapitel auf eine neuere Versionen
- Vorbereitung auf die Unterstützung von BSI Grundschutz++ nach Finalisierung der Methodik
- Auditfertige Reports

TogetherSecure is an official licensee of the IT Baseline Protection Compendium.
Procedure for standard protection with HITGuard
There are many points to consider when building a good ISMS. The IT baseline protection methodology can be seen as a guide to achieving the goal of a sustainable and economical ISMS without major detours.
The best way to see how HITGuard supports you step by step is to use the BSI's recommended procedure for standard protection (see graphic).
1 Assessment of the current situation by means of structural analysis
What are the important business processes in the company? What information is processed and stored in these business processes? What applications do you use to do this? Which IT systems are involved? These are questions that should be asked in the course of surveying the current situation.
"The aim of the structural analysis is to identify those objects and to describe their interaction for which protective measures must be defined in a security concept.
The aim of structural analysis is not to obtain a complete inventory of all the technical components used. Rather, you should sensibly group objects in all sub-surveys" (Source: BSI)
With the BSI baseline protection software HITGuard, you can map your core applications, essential infrastructure services as well as central hardware or other assets of great importance in a graph and relate them to each other. This enables you to carry out target-specific evaluations that provide information about the dependency of processes and services, for example, and check the fulfilment of required recovery times.
2 Assessment of the need for protection
Once the relevant objects have been identified, the next step is to determine the need for protection. The question here is: What damage can occur if the basic values of confidentiality, integrity or availability are violated for an object?
Überlegen Sie hierzu zuerst mögliche Schadensszenarien (z.B. betriebliche Ausfallzeiten, Gesetzesverstöße, persönliche Unversehrtheit, Reputationsverlust). Anschließend bilden Sie mehrere Klassen je nach Größe des möglichen Schadens. Schreiben Sie dazu monetäre Grenzwerte fest, ab der ein Schaden für Sie z.B. überschaubar (< 10.000 €), beträchtlich (< 500.000 €) oder existenzgefährdend (> 500.000 €) ist. Diese Grenzwerte können je nach Unternehmensgröße sehr unterschiedlich sein.
The need for protection of an object basically depends on the need for protection of the business processes and information in which the object is involved. So start identifying the protection needs of your processes, applications, and information. The need for protection is then passed on to the applications, IT systems, network infrastructure, buildings, etc.
HITGuard supports you in many ways: in the creation of the protection requirement classes in the risk policy, in the structured processing of the analyses and in the automatic inheritance of protection requirements
3 Modeling
During modeling, a test plan for the safety requirements of the objects is created based on the structural analysis and the determined protection needs .
At least one IT baseline protection module should be applied to each object of the security concept. To do this, you look at the building blocks of the IT baseline protection compendium individually and consider which objects they can be applied to. Chapter 2.2 of the Compendium provides assistance in this regard.
If no building block could be found for individual objects, a separate risk analysis must be carried out for these objects.
4 IT baseline protection check
Based on the created inspection plan, the objects are now checked. The requirements of the relevant IT baseline protection modules are reviewed question by question. It is determined whether existing security measures are sufficient or whether improvements are needed to achieve the necessary level of protection.
An IT baseline protection module includes basic requirements that must be met in any case, standard requirements for normal protection requirements and more far-reaching security measures for systems with increased protection requirements.
HITGuard offers the contents of the BSI IT Baseline Protection Compendium in the form of structured questionnaires . Through the systematic approach, all necessary security measures are identified. If weaknesses are detected, HITGuard offers you suitable suggestions for measures to reduce or eliminate them.
The results of the checks must be able to be verified later by third parties (e.g. auditors). No problem with our BSI baseline protection software – you receive up-to-date documentation at the click of a mouse.
Das IT-Grundschutz-Kompendium wird kontinuierlich aktualisiert, da sich der Stand der Technik weiterentwickelt. Es muss daher regelmäßig überprüft werden, ob die getroffenen Sicherheitsvorkehrungen noch ausreichen. Hierfür können Sie mit HITGuard die Objekte einer Neubewertung unterziehen. Dabei werden Ihnen Geänderte Vorgaben angezeigt. Für die restlichen Teile können Sie die bestehenden Antworten und Begründungen einfach übernehmen. Dies reduziert Ihren Aufwand erheblich.
Der IT-Grundschutz entwickelt sich weiter. Auch die neue Initiative Grundschutz++ behalten wir im Blick. HITGuard wird diese Weiterentwicklung künftig unterstützen. Da Grundschutz++ aktuell noch nicht final ist und sich inhaltlich noch ändern kann, empfehlen wir für produktive Umsetzungen derzeit weiterhin die Orientierung am etablierten IT-Grundschutz-Kompendium.
5 Risk analysis
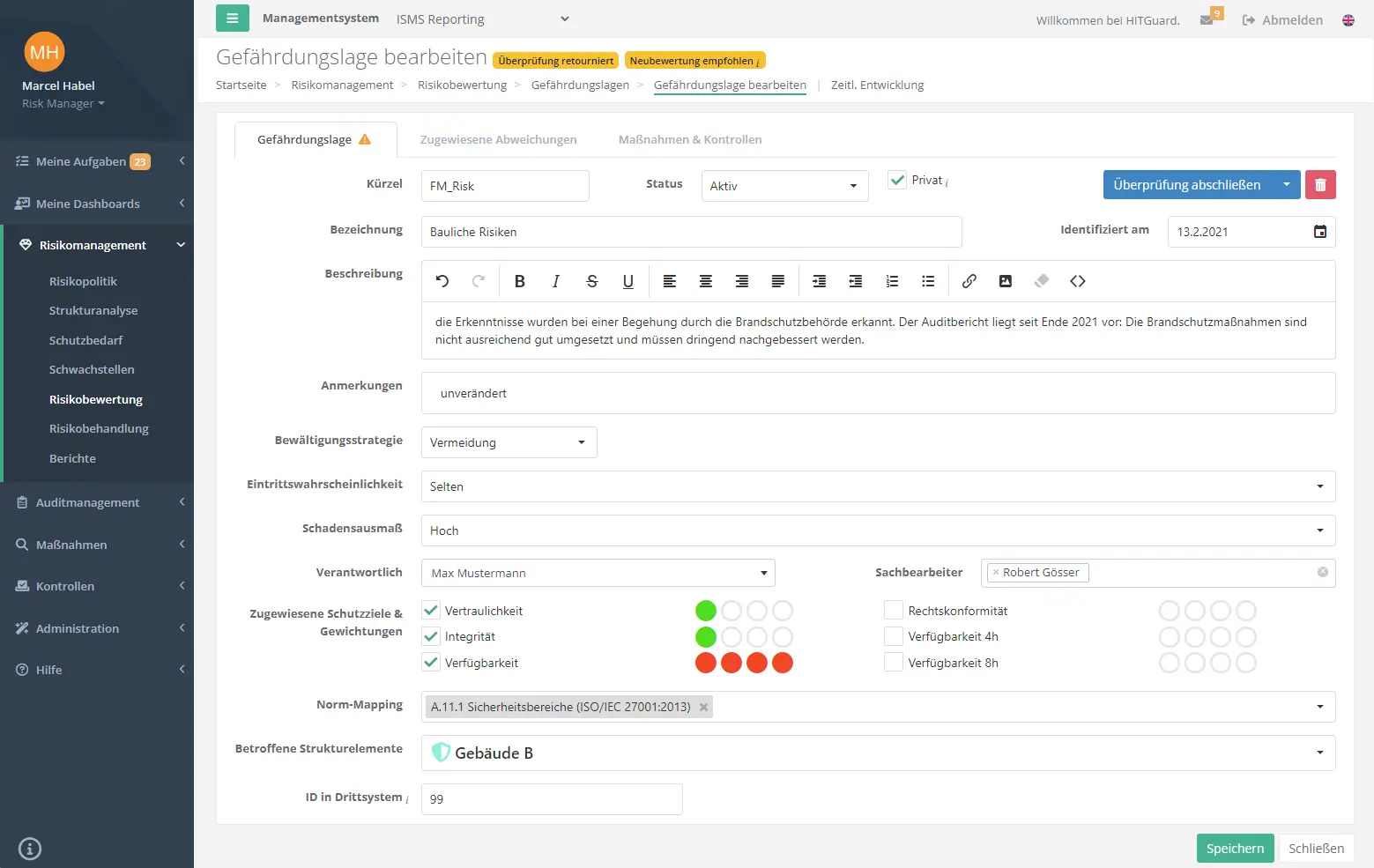
In the next step, vulnerabilities found are converted into risks. In doing so, thematically related weak points are bundled. To help you find out what risks there might be, the IT Baseline Protection Compendium offers a list of 47 threats, which you can find in HITGuard.
Then each risk must be assessed. The magnitude of the risk is determined by its probability of occurrence and the extent of damage to be expected in the event of occurrence. You define the categories you use to describe the probability of occurrence and the extent of damage in the risk policy.
Based on the assessment of the risks, decisions can then be made about their treatment. The visualization in the risk matrix helps to classify and prioritize the risks. If treatment measures are implemented later, they can be used to illustrate their impact on the risk.
6 Implementation of the measures
In most cases, IT baseline protection checks and risk analyses lead to a number of deficits that subsequently need to be remedied. Be it a lack of security measures, a lack of security technology, organizational weaknesses or the like.
The BSI baseline protection tool HITGuard helps you to plan, prioritize and implement measures to close the gaps in the security concept:
- Create measures from suggestions from the IT Baseline Protection Compendium.
- Prioritize actions based on the risk involved.
- Plan the implementation depending on the scope of measure.
- Assign the measures to the responsible persons in the specialist departments and be informed about the progress at definable intervals.
Finally, create controls with which, for example, compliance with guidelines or the patch status of an IT system are regularly checked in the form of recurring tasks.
You can do all this easily and efficiently with HITGuard's workflow-based Internal Control System (ICS).
As mentioned earlier, this is not a one-time path. Plan to carry out the described process continuously and keep your security concept and your security organization up-to-date and secure at all times. Our competent experts will be happy to help you.

Evaluation of the maturity levels of the chapters of the BSI IT Baseline Protection Compendium. (Risk Dashboard)
Request a non-binding demo now
Find out how you can implement the BSI IT baseline protection methodology easily and efficiently with HITGuard
Success story

Emons Holding GmbH & Co. KG
Transport & Logistics Industry
3,650 employees

Emons Freight Forwarding & Logistics
Situation: As an international logistics company, Emons is particularly committed to protecting the critical information assets that form the foundation of successful customer services.
Goal: Implementation of a hybrid information security management system (ISMS) that is largely based on the international family of standards of ISO and the recommendations of the BSI's IT Baseline Protection Compendium.
Implementation: HITGuard offers the possibility of a hybrid implementation. The two information security standards can be used together and in a coordinated manner. You don't have to choose one or the other, but you can use the available norms and standards as well as the knowledge bases available in HITGuard in combination.
Result: Emons was able to achieve the desired results quickly and in a resource-saving manner. Compliance with all internal and external requirements for information security and Data protection with the specifications and recommendations of the two standards is possible at the touch of a button.